Google Security and Codenomicon revealed on Monday that a flaw had existed in OpenSSL for more than two years that could be used to allow anyone (they would have to know the vulnerability existed and be proficient with SSL and network security) on the Internet to read the memory of the systems protected by the vulnerable versions of the OpenSSL software.
OpenSSL is a popular cryptographic library used to digitally encode data as it passes to and from computer servers so that only the intended recipient and sender can make sense of it.
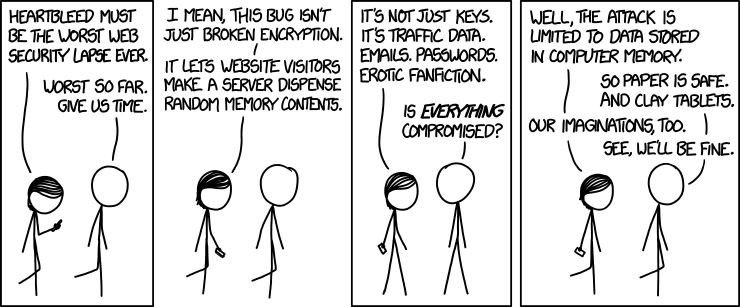
The heartbleed vulnerability enabled attackers to eavesdrop on secure communications and grab 64K of memory from a server. The attack leaves no trace and could be done multiple times to grab a different random 64K of memory. In terms of what could be garnered from this; secret keys used to identify the service providers and to encrypt the traffic, names and passwords, actual data – anything.
What web servers are vulnerable ?
Organisations that used Microsoft’s Internet Information Services (IIS) web server software would not have been affected Codenomicon has noted that more than 66% of the net’s active sites rely on open source alternatives such as Apache and Nginx which do not use OpenSSL so would not be susceptible.
What services are vulnerable ?
This weakness allows stealing the information protected by the SSL/TLS encryption used to secure the Internet. SSL/TLS provides communication security and privacy.
Those at risk include Deutsche Bank, Yahoo and its subsidiary sites Flickr and Tumblr, photo-sharing site Imgur, and the FBI to mention a few. It affects applications such as web, email, instant messaging VPNs. Yahoo was one of the sites worst affected by heartbleed but the firm has now fixed its main services.
CNET have compiled a list of the top 100 services here and whether they are at risk if so if they have been patched.
Is the Nervepoint Access Manager server vulnerable ?
The Nervepoint Access Manager server does not use OpenSSL so is not vulnerable however the webmin service does but:
- this should never be exposed externally the appliance should be firewalled to strictly ports 80/443 only.
- the version in use on the appliance 0.9.8k is not vulnerable as per https://www.openssl.org/news/secadv_20140407.txt. Any upgrades to OpenSSL in the future will bypass the affected versions.
How can I check if any of our own servers are vulnerable?
If you would like to test to see whether a site is exposed by the heartbleed bug you can go here and enter the URL you are concerned about.
Can we get a fix ?
Google warned a select number of organisations about the issue before making it public, so they could update their equipment to a new version of OpenSSL anyone concerned should update to version 1.0.1g released at the start of the week.
Should we change passwords now ?
The initial thought would be to change passwords at once which could make the problem worse if the web server hasn’t been updated to fix the flaw. We recommend waiting until the vulnerability has been patched on service provider’s systems before doing this.

